Network Protocols
Network Protocols
With all the data packets flying around the internet, it’s hard to see how on earth anything gets to where it needs to. In fact, as with all of life, network traffic is only managed successfully through the use of well-defined, universal rules known as protocols.
A network protocol is an agreed way of communicating over a network.
Each protocol should specify the following:
- How to start and end a connection between the devices
- How to start and end messages
- What to do if there is an error in the transmission
- What the data being sent ‘looks’ like i.e. how is it split up
There are at least 35 different standard protocols in use on a day-to-day basis to help manage traffic on the internet. However, you only need to be aware of 10.
- Ethernet
- Wi-Fi
- TCP (Transmission Control Protocol)
- __UDP __(User Datagram Protocol)
- __IP __(Internet Protocol)
- HTTP (Hypertext Transfer Protocol)
- HTTPS (Hypertext Transfer Protocol Secure)
- FTP (File Transfer Protocol)
- email protocols:
- SMTP (Simple Mail Transfer Protocol)
- IMAP (Internet Message Access Protocol).
Connection Protocols - Ethernet and Wi-Fi
Ethernet is a family of related protocols which deal with how data is sent along ethernet cables - it isn’t a single protocol. There are lots of parts to the ethernet protocol family, which include how the hardware is managed, as well as how data is sent and received and how data collisions are managed.
Wi-Fi is also a family of related protocols and deals with how data is sent through wireless connections. In fact, Wi-Fi is a trademark, and the generic term for networks of this nature is WLAN. Any device which has the Wi-Fi logo on it uses the Wi-Fi protocol, and therefore is able to connect wirelessly to other Wi-Fi enabled devices.
Transmission Protocols - TCP and UDP
Both TCP and UDP control how packets are prepared for sending across the internet and what happens to them when they are received on the other side.
TCP is the most widely used of the two, and is also the most reliable. Using TCP, packets are addressed and tracked through the network to make sure that they arrive safely at their destination. Any packets that don’t arrive where they are supposed to be are resent by the sender.
UDP__ __however does away with the packet tracking meaning that everything is sent just once, and if packets don’t arrive, they aren’t resent. The advantage of using UDP is that it is a lot quicker, and so it is often used in online gaming or live streams where quality is less important than speed.
Addressing Protocol - IP
When a device is connected to the internet it is assigned an address called an IP Address. This address may change between connections, but allows all devices to be identified on the internet for the purpose of data packet addressing.
The IP (Internet Protocol) manages the addressing of the data packets, and is responsible for adding the sender and receiver IP addresses to each packet, as well as determining which data packets are addressed for that machine. It works alongside the TCP protocol to ensure that data is sent securely across the internet.
Transfer Protocols - HTTP, HTTPS and FTP
Both HTTP__ and __HTTPS are protocols which are responsible for sending requests for and receiving web pages. HTTP is the protocol which is underlies the World Wide Web, and all websites with___ http:// ___in the address are packaged using the HTTP protocol.
Like HTTP, HTTPS is also responsible for sending and receiving web pages, but provides an encrypted version of HTTP for more secure web transactions. To make sure that you are safe online, you should try to use HTTPS for any webpage that has sensitive data such as usernames or passwords.
FTP is the protocol used to upload or download (i.e. transfer) files between computers and the internet.
Email Protocols - SMTP and IMAP
There are lots of different protocols for sending emails, but you only need to know about SMTP and IMAP.
SMTP is used by mail servers to send and receive mail from all other mail servers around the world.
IMAP__ __controls the download/upload of emails to and from the mail server. It creates a copy of the email on the device that you have, but also leaves a copy on the mail server so that it can be viewed on other devices as well.
TCP / IP Model
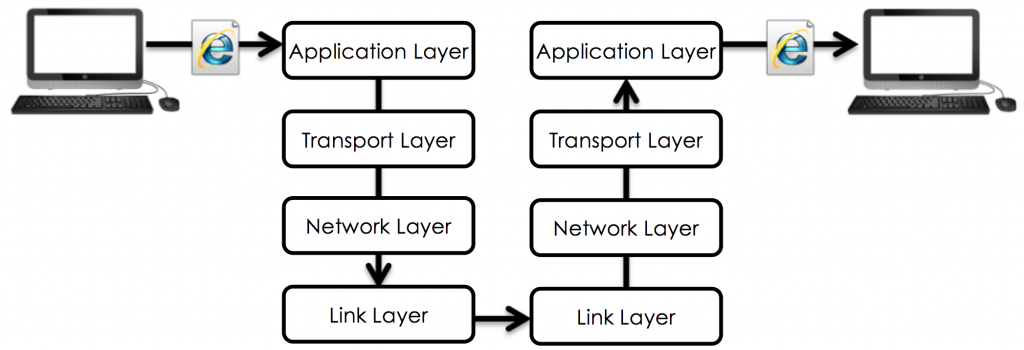
As mentioned above, TCP and IP are two protocols that are used to control communication through the internet. They both work together in the TCP/IP model to ensure that all messages sent from one computer to another arrive safely.
There are four different layers within the TCP/IP model and each layer is responsible for different parts of the communication process.
Splitting the model into layers allow the system to be easily modified as hardware improves:
- application layer
- transport layer
- internet layer
- link layer.
Packets are sent through each layer in turn, before being communicated through the link layer to the receiving device where it goes back through each layer.
Application Layer
This is where the network applications, such as web browsers or email programs, operate. It is also where the transfer (HTTP, HTTPS, FTP) and email (SMTP and IMAP) protocols operate.
Transport Layer
This layer sets up the communication between the two hosts and they agree settings such as ‘language’ and size of packets. This is where the transmission (TCP and UDP) protocols operate.
Internet Layer
This layer addresses and packages data for transmission, and is responsible for routing the packets across the network. This is where the addressing protocol (IP) operates.
Link Layer
This is where the network hardware such as the NIC (network interface card) is located. OS device drivers also sit here.
- State the protocol:Controls how web-pages are sent through the internet.
- HTTP
- State the protocol:Controls how files are uploaded and downloaded on the internet.
- FTP
- State the protocol:Controls how emails are sent between mail servers.
- SMTP
- State the protocol:Controls how data packets are sent through cables.
- Ethernet
- State the protocol:Controls how packets are reliably prepared and sent through the internet.
- TCP
- State the protocol:Controls how web-pages are sent through the internet using encryption.
- HTTPS
- State the protocol:Controls how data packets are sent wirelessly.
- Your answer should include: Wi-Fi / WiFi
- State the protocol:Controls the addressing of packets on the internet.
- IP
- State the protocol:Controls how emails are downloaded from mail servers.
- IMAP
- State the protocol:Controls how packets are quickly prepared and sent through the internet.
- UDP