Network Topologies
Network Topologies
There are lots of different ways computer networks can be joined together. The way in which connections are made between devices is known as a topology. You need to know about two topologies and when you would use them both.
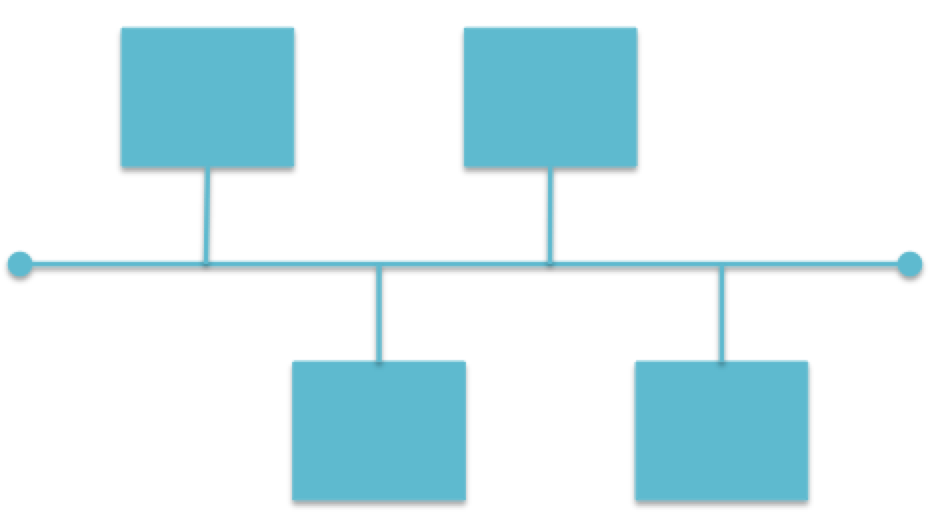
When we describe topologies, we do so using a network diagram. On these, we represent nodes as squares and the connection between the devices as a straight line. You should be careful when answering questions about topologies in exams that you have done what you are asked to do - for example, if you are asked to draw a topology showing four computers, make sure you have only four computers on it.
Bus Topology
A bus topology consists of one long cable with terminators at either end. All the nodes on the network are then connected to this cable by their own separate cable. They are often used when there are only a few computers, or if cost and expertise are limiting factors.
Advantages
- Cheap and easy to set up as it doesn’t require much cabling.
Disadvantages
- Since all data travels along the central cable there is increased chance of data collisions which can cause a network to slow with large numbers of devices connected.
- All data will travel along the main cable, meaning other nodes “see” it, presenting a security risk.
- If the main cable fails, the network will fail.
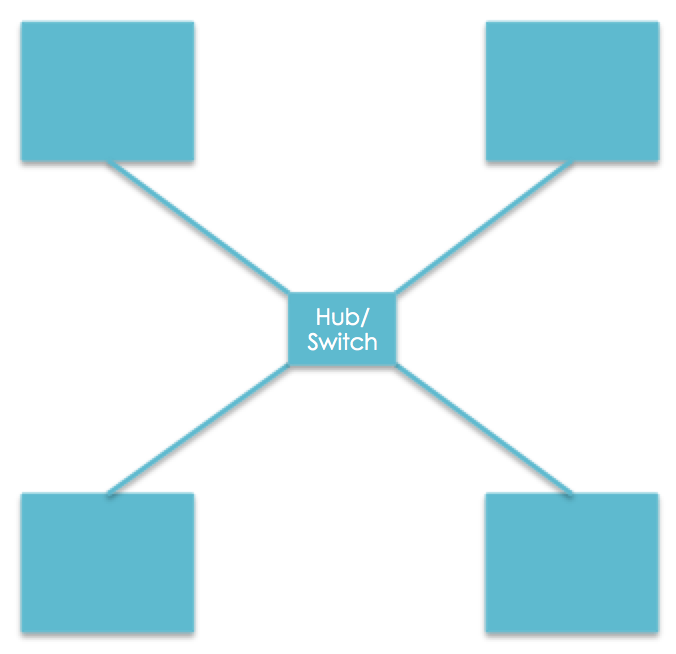
Star Topology
In a star topology, there is a central hub/switch, and all other devices are connected to this one device using its own cable. They are usually used if there are lots of devices or if speed or security is an important factor to consider.
A hub or switch is a device that is used to connect parts of a network together. Switches are intelligent devices that are able to send data packets to just the node that requires it, whereas a hub is passive, and just copies data packets to all ports it is connected to.
4 computer star topology
Advantages
- High performing - tends to be faster than a bus network as there are fewer data collisions.
- Reliable - if one node fails then the others should continue to work.
- Secure (if a switch is used) as the data is only sent to the devices that should have access to it.
Disadvantages
- Uses a lot of cable so is expensive to set up, and requires more expertise than a bus network.
- Requires additional hardware in the form of a hub or switch which also makes it more expensive.
- High reliance on the central hub/switch. If this fails, the network fails.
- Security issues if a hub is used, as this will send data to all nodes connected to the network.
- Would a Bus or Star would be most appropriate?Small office with limited budget and only a couple of computers.
- Bus
- Would a Bus or Star would be most appropriate?Workplace dealing with confidential documents.
- Star
- Would a Bus or Star would be most appropriate?A large investment bank which relies on fast access to the network at all times.
- Star